Insider Threat Policy Template
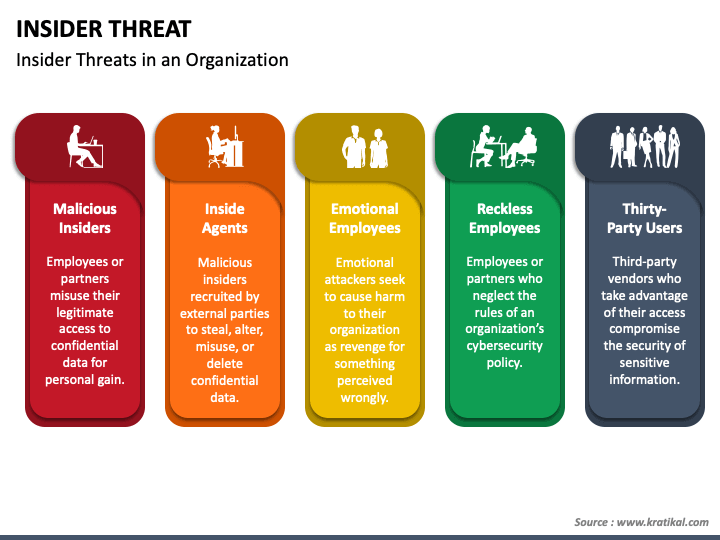
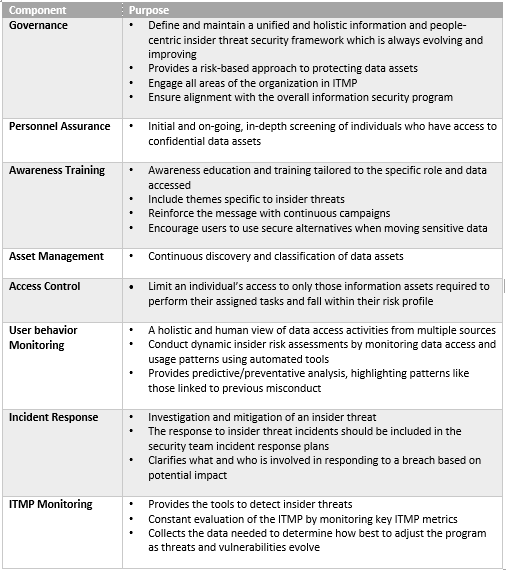
Insider Threat Policy Template - Activities that they are otherwise not able to perform under applicable law, regulation, and policy. A malicious insider threat to an organization is a current or former employee, contractor, or other business partner who has or had authorized access to an organization's network, system, or data and intentionally exceeded or misused that access in a manner that negatively affected the confidentiality, integrity, or availability of the organization's information or information systems. Cisa recently released the “2024 u.s. Controlled and managed by the. Federal and dod policies establish minimum standards for insider threat programs in government agencies, dod components, and cleared industry. • provide copies of the insider threat plan upon request and will make the plan available to the dss during the security vulnerability assessments (sva). It should be customized to fit the specific requirements and context of each organization, and its implementation should be accompanied by regular training and awareness programs. The forms are downloadable and the data collected is. This insider threat policy template provides a framework for organizations to develop robust measures against threats from within. It is not intended for use as a template. Cisa recently released the “2024 u.s. Activities that they are otherwise not able to perform under applicable law, regulation, and policy. Included in this comprehensive resource were the insider threat reporting templates. As an example of an insider threat, in 2024, authorities charged a former google employee with stealing confidential trade secrets tied to the company’s artificial intelligence technology. On june 13, 2024, cisa, fbi, dhs office of intelligence and analysis, and the u.s. Insider threat reporting template workplace reporting form the reporting and investigative templates are not intended to provide any organization with the authority to perform. Controlled and managed by the. It is not intended for use as a template. A malicious insider threat to an organization is a current or former employee, contractor, or other business partner who has or had authorized access to an organization's network, system, or data and intentionally exceeded or misused that access in a manner that negatively affected the confidentiality, integrity, or availability of the organization's information or information systems. This template is tailored to meet the specific requirements of the department of defense (dod) and is compliant with federal regulations, making it a. This template is tailored to meet the specific requirements of the department of defense (dod) and is compliant with federal regulations, making it a. Cisa is releasing these templates as standalone products, to help organizations manage the risk of insider threats. Included in this comprehensive resource were the insider threat reporting templates. It should be customized to fit the specific. Controlled and managed by the. This template is tailored to meet the specific requirements of the department of defense (dod) and is compliant with federal regulations, making it a. Regular risk assessments and audits should be conducted to ensure the program’s effectiveness and identify any vulnerabilities or areas for improvement. Establish an insider threat program based on the organization’s size.. It should be customized to fit the specific requirements and context of each organization, and its implementation should be accompanied by regular training and awareness programs. Activities that they are otherwise not able to perform under applicable law, regulation, and policy. The forms are downloadable and the data collected is. Insider threat reporting template workplace reporting form the reporting and. Provide copies of the insider threat program plan upon request and make the plan available to the dcsa industrial security representative (isr) during the security review and rating process. The forms are downloadable and the data collected is. The nittf aims to develop an insider threat program that:. Insider risk management supports up to twenty policies for each policy. Federal. Cisa recently released the “2024 u.s. This template is tailored to meet the specific requirements of the department of defense (dod) and is compliant with federal regulations, making it a. Election assistance commission released the 2024 u.s. On june 13, 2024, cisa, fbi, dhs office of intelligence and analysis, and the u.s. This insider threat policy template provides a framework. As an example of an insider threat, in 2024, authorities charged a former google employee with stealing confidential trade secrets tied to the company’s artificial intelligence technology. Activities that they are otherwise not able to perform under applicable law, regulation, and policy. Establish an insider threat program based on the organization’s size. It is not intended for use as a. Record of organizational actions related to an insider threat incident, promote accountability of necessary steps to protect assets, and to identify vulnerabilities in the effort of mitigating future insider threats. Insider risk management supports up to twenty policies for each policy. Additional nittf guides and templates. Controlled and managed by the. This job aid provides a sample of how a. Provide copies of the insider threat program plan upon request and make the plan available to the dcsa industrial security representative (isr) during the security review and rating process. On june 13, 2024, cisa, fbi, dhs office of intelligence and analysis, and the u.s. The forms are downloadable and the data collected is. Controlled and managed by the. This product. Sample insider threat program plan for industry december 2022, 10 pages. This template is tailored to meet the specific requirements of the department of defense (dod) and is compliant with federal regulations, making it a. Federal and dod policies establish minimum standards for insider threat programs in government agencies, dod components, and cleared industry. Election assistance commission released the 2024. It also provides additional guidance and resources for developing a plan. Insider risk management supports up to twenty policies for each policy. Record of organizational actions related to an insider threat incident, promote accountability of necessary steps to protect assets, and to identify vulnerabilities in the effort of mitigating future insider threats. Election assistance commission released the 2024 u.s. Activities. Election assistance commission released the 2024 u.s. Cisa is releasing these templates as standalone products, to help organizations manage the risk of insider threats. Additional nittf guides and templates. This product is widely applicable across the critical infrastructure community. A presidential memorandum, the national insider threat policy and the minimum standards, was issued in november 2012 to establish common expectations and best practices. Sample insider threat program plan for industry december 2022, 10 pages. Included in this comprehensive resource were the insider threat reporting templates. Regular risk assessments and audits should be conducted to ensure the program’s effectiveness and identify any vulnerabilities or areas for improvement. • provide copies of the insider threat plan upon request and will make the plan available to the dss during the security vulnerability assessments (sva). It is not intended for use as a template. Each policy must have a template assigned in the policy creation workflow before the policy is created. Developing an insider threat program involves establishing policies and procedures to mitigate the risk of insider threats, including implementing user activity monitoring as a key component. This insider threat policy template provides a framework for organizations to develop robust measures against threats from within. It also provides additional guidance and resources for developing a plan. Record of organizational actions related to an insider threat incident, promote accountability of necessary steps to protect assets, and to identify vulnerabilities in the effort of mitigating future insider threats. This job aid provides a sample of how a plan can be tailored to the specific insider threat program procedures and processes in place at your company.How to Establish an Effective Insider Threat Program
Insider Threat Policy Template
Insider Threat Plan Template
Best Practices for Developing an Insider Threat Program Adamo
Insider Threat Program Template
Insider Threat Policy Template
Insider Threat Policy Template
Insider Threat Plan Template
Insider Threat Program Template
Insider Threat Program Template
The Insider Threat Guide,” Which Includes Two “Insider Threat Reporting Templates” That Are Widely Applicable Across The Critical Infrastructure Community.
Insider Risk Management Supports Up To Twenty Policies For Each Policy.
This Template Is Tailored To Meet The Specific Requirements Of The Department Of Defense (Dod) And Is Compliant With Federal Regulations, Making It A.
Controlled And Managed By The.
Related Post: